Ubuntu infrastructure has been down for more than a day

Ubuntu and Canonical servers were knocked offline by a sustained, cross-border DDoS attack, disrupting access to critical websites and security communications. The outage coincided with the release of exploit code for a major Linux vulnerability, hampering Ubuntu's ability to issue guidance. While mirror sites continue to provide updates, the attackers—linked to a pro-Iranian group—used a 'stressor' service to carry out the attack.
- ▪Ubuntu and Canonical servers have been down for over 24 hours due to a sustained DDoS attack.
- ▪A pro-Iranian group claimed responsibility, using a 'stressor' service called Beam to carry out the attack.
- ▪Critical Ubuntu websites like security.ubuntu.com and ubuntu.com remain inaccessible, though mirror sites still provide updates.
- ▪The outage began shortly after public release of exploit code allowing untrusted users to gain root access on Linux systems, including Ubuntu.
- ▪Stressor or booter sites have long enabled DDoS attacks and remain operational despite law enforcement efforts.
Opening excerpt (first ~120 words) tap to expand
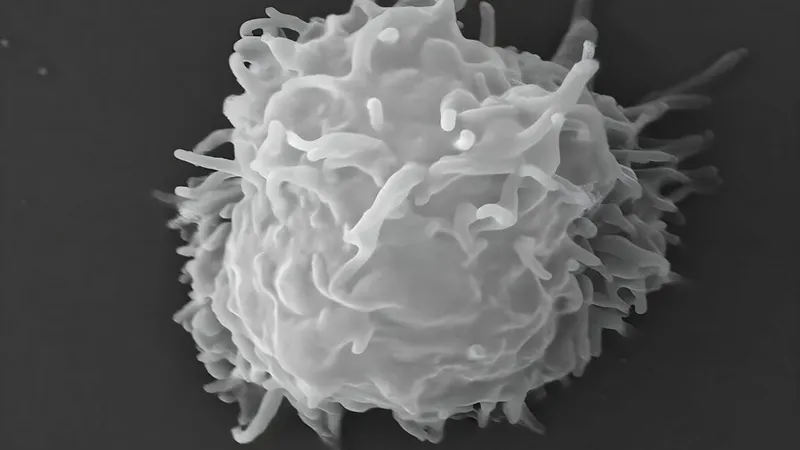
COME BACK LATER Ubuntu infrastructure has been down for more than a day The outage has hampered communication concerning a critical vulnerability that gives root. Dan Goodin – May 1, 2026 3:12 pm | 5 An iteration of what happens when your site gets shut down by a DDoS attack. An iteration of what happens when your site gets shut down by a DDoS attack. Text settings Story text Size Small Standard Large Width * Standard Wide Links Standard Orange * Subscribers only Learn more Minimize to nav Servers operated by Ubuntu and its parent company Canonical were knocked offline on Thursday morning and have remained down ever since, a situation that’s preventing the OS provider from communicating normally following the botched disclosure of a major vulnerability.
…
Excerpt limited to ~120 words for fair-use compliance. The full article is at Ars Technica - All content.