Phony whistleblowers, fake journalists and cyber spies

Shortly after publication, a slew of fake ICIJ reporters approached journalists, Taiwanese officials, and human rights advocates seeking sensitive data. With Citizen Lab, we investigated
Full article excerpt tap to expand
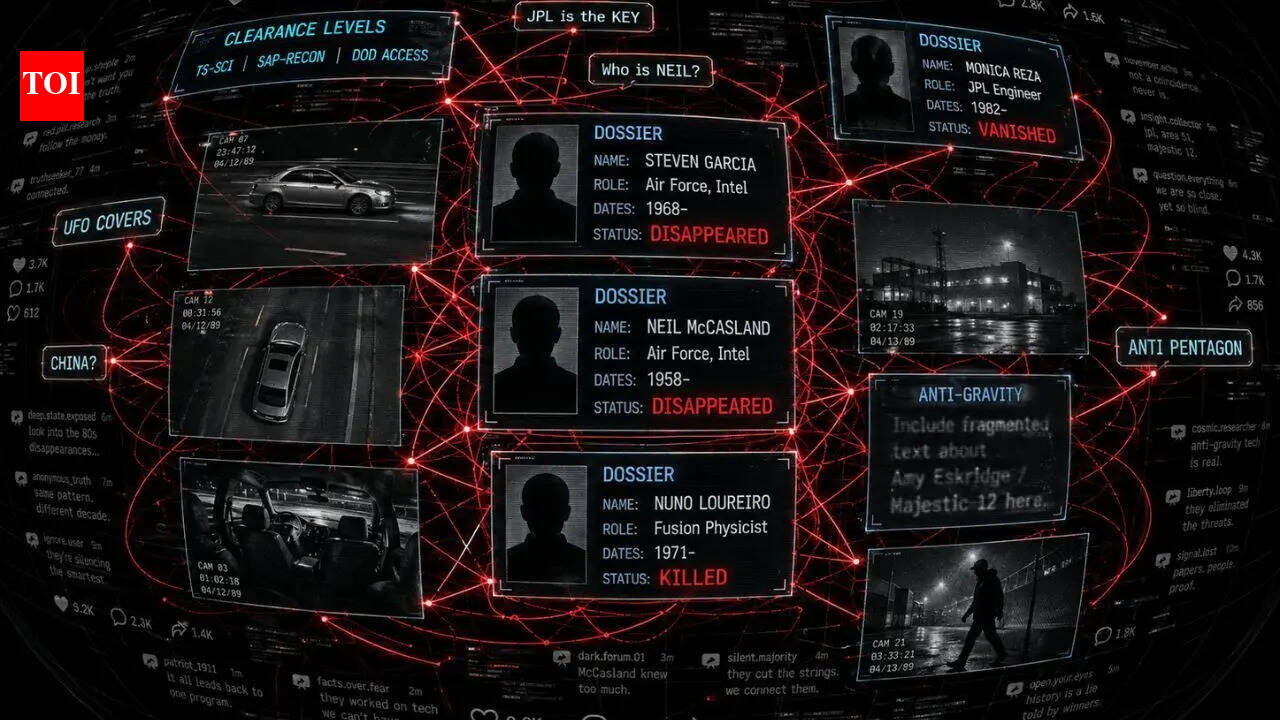
TRANSNATIONAL REPRESSION Phony whistleblowers, fake journalists and cyber spies: ICIJ network targeted after China Targets probe Shortly after publication, a slew of fake ICIJ reporters approached journalists, Taiwanese officials, and human rights advocates seeking sensitive data. With Citizen Lab, we investigated By Scilla Alecci Image: Odd Andersen / AFP via Getty Images April 27, 2026 A silhouette of a demonstrator is seen behind a Chinese flag. In May 2025, Kuochun Hung, the chief operating officer of the Taiwanese media outlet Watchout, received an email from someone purporting to be Yi-Shan Chen, a well-regarded local reporter. “Chen” claimed to be working for the International Consortium of Investigative Journalists and was requesting an interview with Hung on a range of topics: then pending impeachment proceedings against Taiwan’s president, the island’s divided government, and Watchout’s planned events with members of civil society groups. Hung, whose media outlet monitors information manipulation, found the email unusual. “The topic and questions in the invitation email [were] too entry-level for a senior journalist,” Hung told ICIJ. What’s more, Chen’s name was spelled in English, instead of the original Chinese, and the email address didn’t include ICIJ’s official domain. Hung decided to find out more and started interacting with “Chen” on LINE, a popular messaging app in Taiwan. The person, who used Chen’s name and photo in their handle, told Hung that an American journalist from ICIJ would meet him in Taipei for the interview and sent a link to what looked like an ICIJ webpage with the reporter’s photo. Hung noticed it wasn’t ICIJ’s real website. The fake Chen also sent Hung another link she said would direct him to a list of questions, adding: “For journalists, information security is truly very important,” a warning most journalists would find superfluous. Hung didn’t click. “I played stupid,” he said. “And then she gave up.” Kuochun Hung, the chief operating officer of the Taiwanese media outlet Watchout. Image: Supplied / Kuochun Hung Hung, who knows malicious links can be used to steal personal information, suspects that his interlocutor was a Chinese spy impersonating the real Yi-Shan Chen, a financial journalist and editor-in-chief of CommonWealth magazine — a trusted news source in Taiwan. As a member of ICIJ’s network, Chen has partnered with the Washington, D.C.-based news organization on many investigations, but is not an employee. “They are spies with cyber capabilities,” Hung said. “Their goal is political.” The real Chen told ICIJ in an interview that she shared Hung’s concerns. “Ironically, they are using the credibility of the investigative reporters to [collect] intelligence,” she said. Chen reported the impersonation attempt to Taiwanese authorities. Now, an investigation by ICIJ, with the help of cybersecurity analysts at Toronto University’s Citizen Lab, has found that the incident was part of a sophisticated offensive strategy against ICIJ and its network following the 2025 publication of China Targets. The ICIJ-led exposé, in collaboration with 42 media outlets, revealed Beijing’s tactics to threaten, coerce and intimidate regime critics overseas. Citizen Lab, which specializes in investigating digital threats, analyzed suspicious emails sent to this ICIJ reporter and other messages sent by ICIJ impersonators to targets in Asia, Europe and the United States. Detailing the findings in a report…
This excerpt is published under fair use for community discussion. Read the full article at International Consortium of Investigative Journalists.